IT Architectural Plan & Implementation
Executive Summary
This document provides a practical, phased IT architectural plan and implementation roadmap suitable for a mid-sized organization (50–500 users). It covers objectives, assumptions, target architecture (logical & physical), network and security design, data management, backup & disaster recovery, operations (monitoring, patching), implementation timeline, roles, risk register, KPIs, and templates you can reuse.
Note: This is a generic, ready-to-use plan. For a tailored plan, provide specifics (number of users, current systems, cloud vs on-prem split, budget). However, you can implement this as-is for a standard modernization project.
1. Objectives
- Provide a resilient, secure, and scalable IT architecture.
- Ensure high availability for business-critical services (99.95% target).
- Improve security posture with zero-trust principles.
- Centralize management and monitoring for operational efficiency.
- Implement backup and disaster recovery with RTO ≤ 4 hours and RPO ≤ 1 hour for critical systems.
- Enable future cloud adoption and automation.
2. Scope
- Users: 50–500
- Services: Email, file shares, business apps (ERP/CRM), web apps, directory services, endpoints, Wi‑Fi, VoIP, printing
- Environments: Production, Staging, Development
- Infrastructure: On-prem datacenter + hybrid cloud (preferred)
3. Key Assumptions
- Internet connection: redundant links available.
- The organization will adopt a hybrid cloud model (some workloads on AWS/Azure/GCP).
- Existing systems include Windows AD or Azure AD; migration is possible.
- Budget allows phased spending across 6–9 months.
4. Current-State (Example baseline)
- Single on-prem datacenter with 2 racks.
- Windows Server domain controllers (2), file server, virtualization host (2), backup server (legacy), firewall (single), unmanaged Wi‑Fi.
- No centralized monitoring, ad-hoc patching, and backups not tested regularly.
5. Target Architecture (Logical)
- Identity & Access: Centralized Identity (Azure AD or AD DS + ADFS/SSO), MFA, role-based access control (RBAC).
- Network: Edge firewalls, DMZ for public services, internal segmented network (VLANs for users, servers, printers, IoT, voice), VPN gateways for remote users.
- Compute: Virtualization cluster(s) + hybrid cloud VMs/containers for burst and DR.
- Storage: SAN/NAS on-prem + cloud object storage for backups/archives.
- Data Services: Database cluster(s), replicated where needed.
- Security: Next‑gen firewall, IDS/IPS, endpoint protection (EDR), centralized logging (SIEM), CASB for cloud apps.
- Management: Patch management, configuration management (IaC for cloud), centralized monitoring (observability stack), ITSM (tickets, CMDB).
6. Target Architecture (Physical / Topology)
- Edge: 2x ISP links → Load-balanced Edge Firewalls (HA pair) → Core Switches (L3)
- Core: Core Switch → Distribution switches → Access switches (VLANs)
- Servers: Virtualization cluster (3+ hosts) with shared storage (HA)
- DMZ: Web/public services in DMZ, reverse proxy/load balancer
- Cloud: Dedicated VPC/Subscription with secure peering/VPN to on-prem
Internet — ISP1/ISP2
|
Edge Firewalls (HA)
|
Core Router
/ | \
DMZ Internal VPN Gateway
| VLANs
Web/VPN App/DB/Files
Servers Servers
7. Network Segmentation (VLANs)
- VLAN 10 — Management
- VLAN 20 — Servers
- VLAN 30 — Users
- VLAN 40 — Guest Wi‑Fi
- VLAN 50 — IoT/Printers
- VLAN 60 — Voice
- DMZ — Public-facing services
8. Security Architecture
- Zero Trust: Verify every access request. Implement MFA and least privilege.
- Perimeter: NGFW with application-aware policies.
- Host Security: EDR on all endpoints and servers.
- Identity: Azure AD + Conditional Access or AD with MFA gateway.
- Encryption: TLS for all in-transit; AES-256 for at-rest storage.
- Logging: Send logs to centralized SIEM; retain per policy (e.g., 1 year hot, 3 years cold).
- Vulnerability Management: Weekly scans, monthly patch cycles, emergency patching for critical CVEs.
- Secure SDLC: If apps are built in-house, integrate SAST/DAST in CI/CD.
9. Data Management & Backup
- Data classification: Public, Internal, Confidential, Restricted.
- Backup strategy:
- Critical systems: snapshot-based + transaction log shipping (RPO ≤ 1h).
- Full backups weekly, incremental daily.
- Offsite copies to cloud object storage with immutability (WORM) for 90+ days.
- Disaster Recovery:
- Warm standby in cloud for critical workloads.
- DR runbook, quarterly DR tests, maintain RTO ≤ 4 hours for critical apps.
10. Monitoring & Observability
- Infrastructure metrics (CPU, RAM, Disk, Network)
- Application performance monitoring (APM)
- Log aggregation (SIEM) and alerting
- Uptime checks and synthetic transactions
- SLOs/SLA dashboards for exec reporting
11. Operations & Automation
- Patch Management: WSUS/Intune for Windows, repo-based for Linux (with automation)
- Configuration Management: Use Ansible/Terraform for infrastructure as code
- CI/CD: Jenkins/GitHub Actions/GitLab CI for app deployments.
- ITSM: ServiceNow/Jira Service Management for ticketing and change control
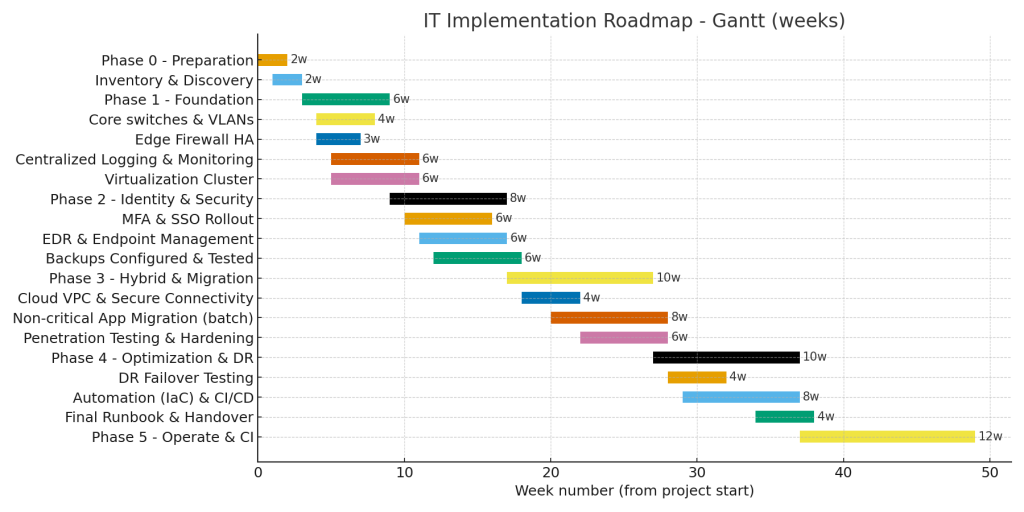
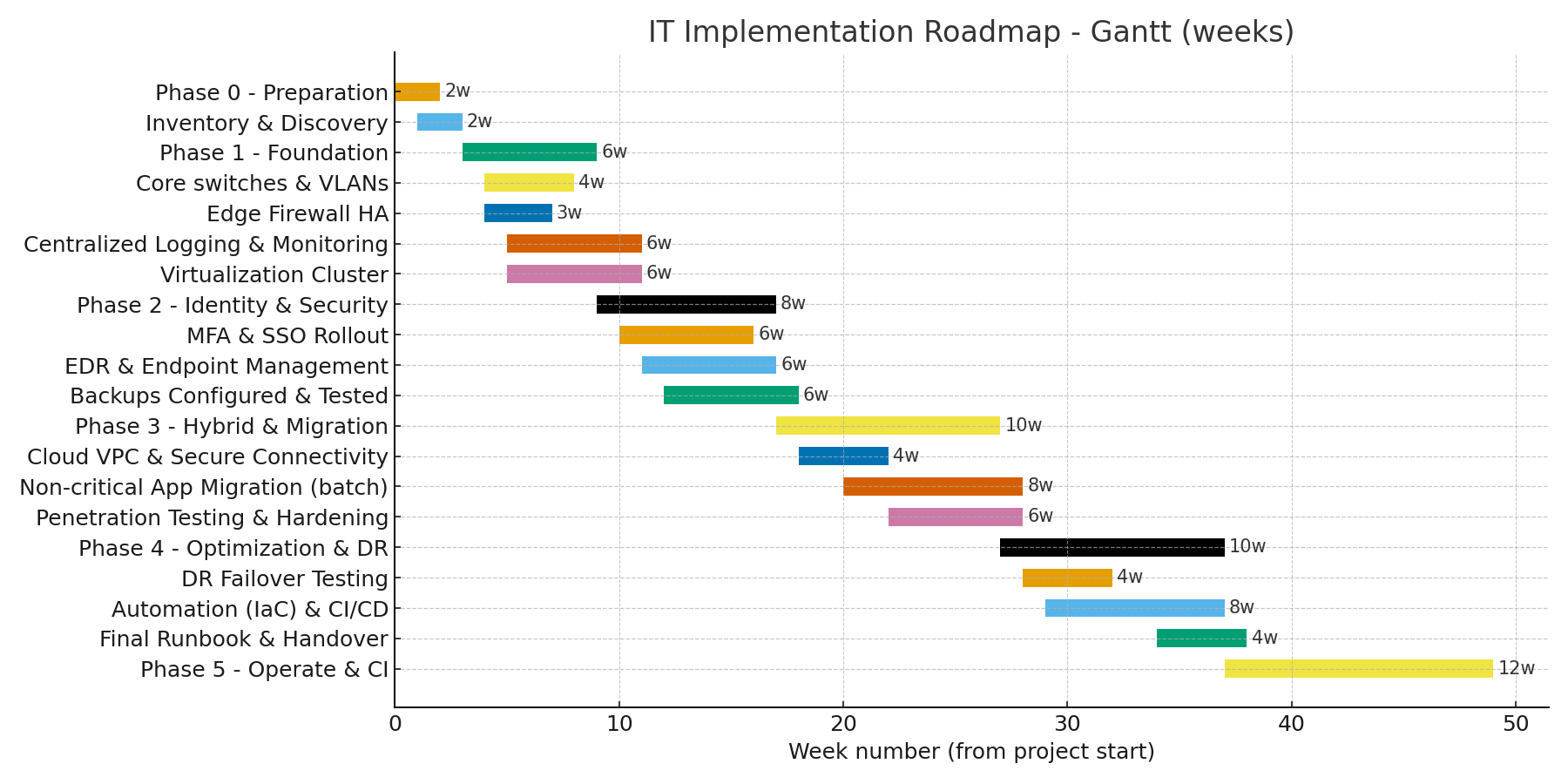
12. Implementation Roadmap (Phased)
Phase 0 — Preparation (Weeks 0–2)
- Stakeholder alignment, finalize scope and budget
- Inventory and discovery (hardware, software, accounts)
- Risk assessment and compliance mapping
Phase 1 — Foundation (Weeks 3–8)
- Procure hardware & cloud accounts
- Deploy edge firewalls in HA
- Implement core switches and VLANs
- Harden and deploy virtualization cluster
- Setup centralized logging and monitoring
Phase 2 — Identity, Security & Core Services (Weeks 9–16)
- Deploy centralized identity (Azure AD/AD sync)
- Roll out MFA and SSO for critical apps
- Deploy EDR and endpoint management
- Migrate file shares and business apps to virtualized environment
- Configure backups and initial backup runs
Phase 3 — Hybrid & Application Migration (Weeks 17–26)
- Create cloud VPC and secure connectivity (VPN or ExpressRoute/Direct Connect equivalent)
- Migrate non-critical apps to cloud in batches
- Implement CASB and data loss prevention (DLP)
- Conduct security hardening and penetration testing
Phase 4 — Optimization & DR (Weeks 27–36)
- Implement automation (IaC) and CI/CD pipelines
- DR failover testing and runbook updates
- Fine-tune monitoring and SLO dashboards
- Staff training and handover
Phase 5 — Operate & Continuous Improvement (Ongoing)
- Regular patching, quarterly DR tests, continuous vulnerability management
- Monthly performance and security reviews
13. Milestones & Deliverables
- Inventory report (end Week 2)
- Network baseline & VLAN config (end Week 6)
- Identity & MFA rollout (end Week 12)
- Backup & DR tested (end Week 28)
- Final runbook & handover (end Week 36)
14. Roles & Resource Plan
- Project Sponsor (executive)
- Project Manager
- Solution Architect (lead)
- Network Engineer(s)
- Security Engineer(s)
- Systems Administrator(s)
- Cloud Engineer
- Application Owners
- Vendor/Integrator (optional)
15. Estimated Budget Template (example numbers)
These are ballpark figures — replace with vendor quotes.
- Core networking (firewalls, switches): $40k–$120k
- Servers & storage (HA): $50k–$150k
- Backup & replication solution: $10k–$50k
- Cloud monthly (small footprint): $1k–$5k/mo
- Security tooling (EDR, SIEM, IAM): $20k–$80k
- Professional services/implementation: $30k–$120k
16. Risk Register (Top items)
- Single point of failure — mitigate with HA for edge & core.
- Data loss — mitigate with tested backups and offsite copies.
- Insider threat — mitigate with RBAC, logging, least privilege.
- Insufficient staff skills — mitigate with vendor support and training.
- Budget overrun — phased procurement and MVP approach.
17. KPIs & Success Metrics
- System uptime: target 99.95% for critical systems
- Time to patch critical vulnerabilities: ≤ 72 hours
- Mean time to recover (MTTR): ≤ 4 hours for critical failures
- % of endpoints with EDR installed: 100%
- Backup success rate: ≥ 99% weekly
18. Policies & Standards (short list)
- Acceptable Use Policy
- Access Control Policy
- Backup and Retention Policy
- Incident Response Plan
- Change Management Policy
- Data Classification Policy
19. Sample Implementation Checklist
- Inventory completed
- Backup plan documented and initial backups successful
- Firewalls deployed & baseline rules implemented
- VLANs provisioned and tested
- AD/Azure AD configured with MFA
- EDR deployed to all endpoints
- SIEM ingesting logs from core devices
- DR runbook created and tested
20. Next Steps (recommended)
- Approve the plan and budget.
- Run a 2-week discovery to gather exact counts, apps, and dependencies.
- Finalize cloud vendor and procurement list.
- Kick off Phase 0 with project governance.
Appendix A — Quick configuration examples
Example: VLAN interface (Cisco,Juniper IOS)
interface Vlan10
description Management
ip address 10.0.10.1 255.255.255.0
interface Vlan30
description User VLAN
ip address 10.0.30.1 255.255.255.0
Example: Basic backup retention policy
- Daily incremental (retain 14 days)
- Weekly full (retain 12 weeks)
- Monthly full (retain 12 months)
- Offsite cold archive (retain 7 years for compliance)
Produce network diagrams in PNG/SVG.
- Produce a detailed bill of materials (BOM) with vendor models and costs.
- Create a week-by-week Gantt chart for project management.
https://shorturl.fm/8jeuI
https://shorturl.fm/PCawh
https://shorturl.fm/gMLeU
https://shorturl.fm/5TvKA
https://shorturl.fm/gSFo9
https://shorturl.fm/PoTF8
https://shorturl.fm/bkCS7
https://shorturl.fm/3X1ZO
https://shorturl.fm/cc2ku
https://shorturl.fm/ND8wY
https://shorturl.fm/K1VtX
https://shorturl.fm/Q8tLC
Share your link and rake in rewards—join our affiliate team!
Get paid for every referral—enroll in our affiliate program!
Share your unique link and cash in—join now!
Maximize your earnings with top-tier offers—apply now!